Securing the Internet of Things (IoT) Ecosystem
Safeguard the interconnected world of IoT devices.
Challenge
In the dynamic landscape of the IoT, the integrity of every device hinges on the strength of its underlying hardware security. Ensuring the security and integrity of IoT devices that are often built with cost and convenience in mind, not security, is critical to protecting the vast amounts of data they generate from sophisticated cyber threats.
Vulnerability of Interconnected Systems
IoT devices range from simple home sensors to complex industrial controllers. The diversity and scale of these devices introduce multiple vulnerabilities, especially in systems where security has not been prioritized.
Protection of Sensitive Information
IoT devices generate and transmit sensitive data, which must be protected against interception and unauthorized access to maintain user privacy and data integrity.
Enabling Lifecycle and Supply Chain Security
The lifecycle of IoT devices involves various stages, from manufacturing to deployment, and eventual decommissioning. Robust hardware security practices ensure that devices are secure at every step., IoT devices must maintain a strong security posture, even as they pass through various hands in a complex supply chain.
How Radix Helps IoT Security
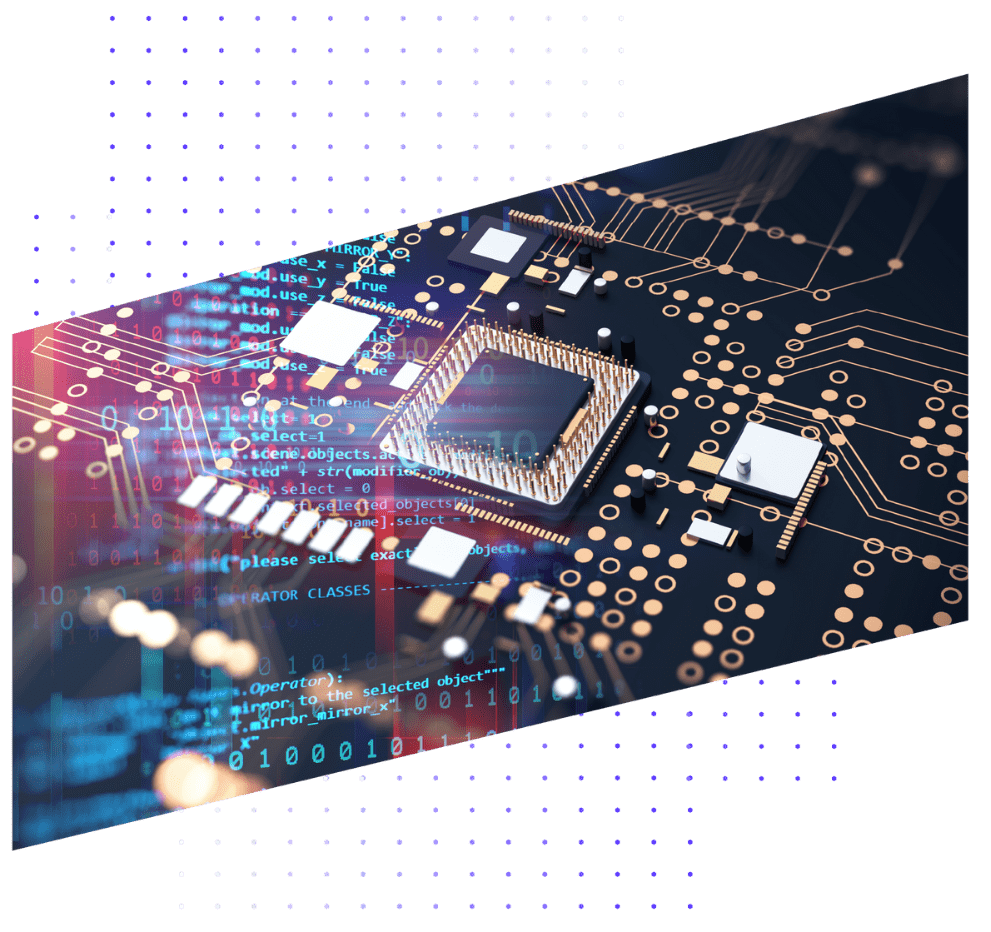
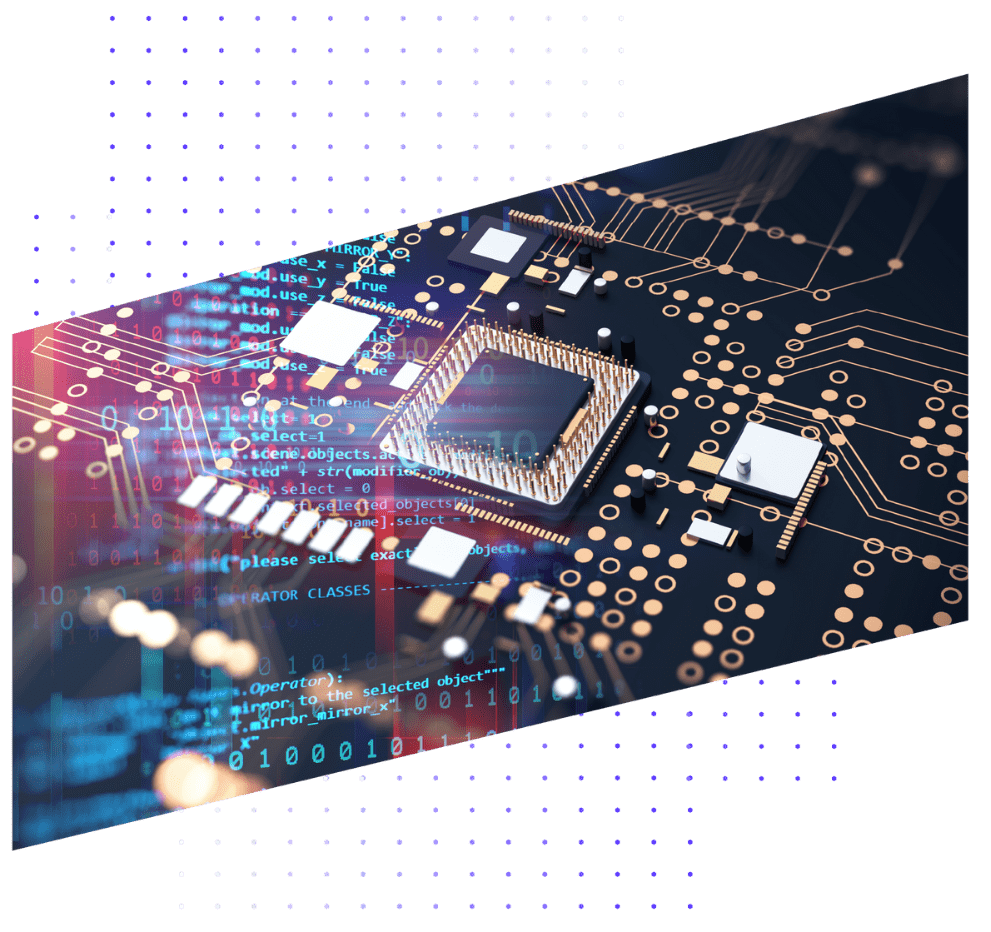
System-On-Chips
Fundamental to the security of IoT, automotive, and datacenters is the security of the SoCs that power them. Verify the security of increasingly complex SoCs with Radix.
Roots of Trust
Hardware roots of trust have become the foundation of semiconductor security. See how you can build a more secure system with hardware security assurance from Cycuity.
CWE
The industry’s formal list of common hardware weaknesses is the Common Weakness Enumeration, a list created and curated by MITRE. For organizations seeking a “secure by design” approach, testing against the CWE list is critical.
Application Processors
Modern microprocessors are core to the applications that power cars, data centers, and mobile phones. As their performance has grown, so have their vulnerabilities.
Related Resources
See How Radix Can Improve Your IoT Hardware Security
Strengthen IoT Ecosystems with Radix: Deploy Hardware Security for Smart, Connected Devices.

