Roots of Trust
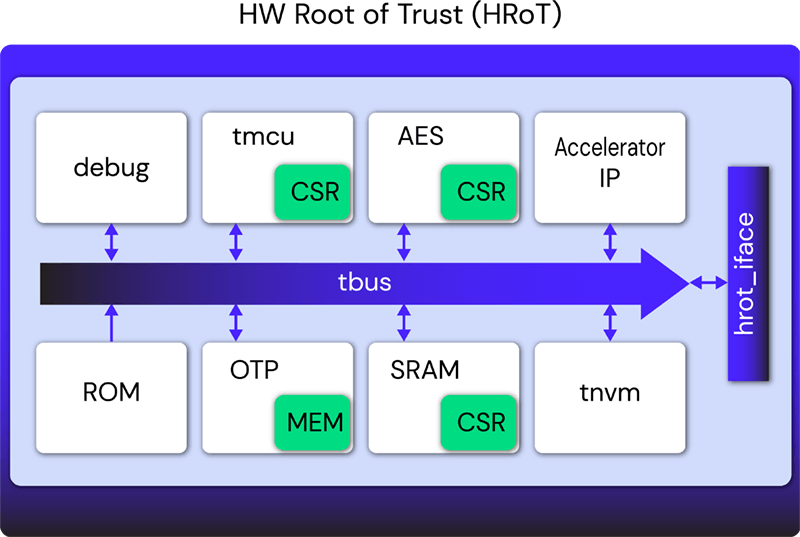
Hardware roots of trust are becoming commonplace to establish a chain of trust for system security starting in hardware.
Hardware roots of trust are becoming commonplace to establish a chain of trust for system security starting in hardware. Hardware roots of trust provide invaluable security features that support:
- Secure Boot: Roots of trust manage the encryption and authentication key assets and cryptographic functions to ensure systems are booted securely. Radix is effective at identifying secure design assets and ensuring they are properly managed during secure boot.
- Secure Enclave: Highly privileged executions often require hardware-based protections. Hardware roots of trust are often used to ensure secure code is isolated from the rest of the system to avoid confidentiality or integrity violations. Radix can ensure that data stored within the secure enclave cannot be accessed or be observed through any side effects.
- Anti-tamper Resistance: Roots of trust often provide the anti-tamper mitigations to prevent adversaries from physically attacking the device. Ensuring that anti-tamper mitigations are applied properly is critical for them to operate securely.
Our firmware configures the hardware roots of trust and its surrounding system, so it is imperative for both features to undergo a stringent security verification process. Tortuga Logic’s Radix series addresses our need for concurrent firmware and hardware validation to ensure we deliver the most secure products to the markets we serve, including aerospace and defense, automotive, and datacenter.
Gaurav Singh, Corporate Vice President, Silicon Architecture and Verification, Xilinx

Level up your hardware security today.
Get the confidence of end-to-end hardware security assurance throughout the product lifecycle. Contact us today to see how.
